The first question most compliance officers ask when they hear "autonomous Oracle support" is: what happens to the audit trail? If an AI system is executing fixes to Oracle EBS — altering tablespaces, updating interface tables, rerunning concurrent programs — who is responsible? Who approved it? What exactly ran? How do you demonstrate to an auditor that the change was authorized, documented, and controlled?
These are the right questions. SOX Section 404 and ITGC Change Management controls exist precisely because uncontrolled changes to financial systems create material risk. An Oracle EBS system that processes invoices, manages the general ledger, and controls period close is a financial reporting system. Changes to it require evidence of authorization, review, and documentation.
The Oracle AI platform is designed to produce a stronger audit trail than manual DBA processes — not as an afterthought, but as a core architectural requirement. Every element of the compliance posture is built into the platform's execution path, not bolted on afterward.
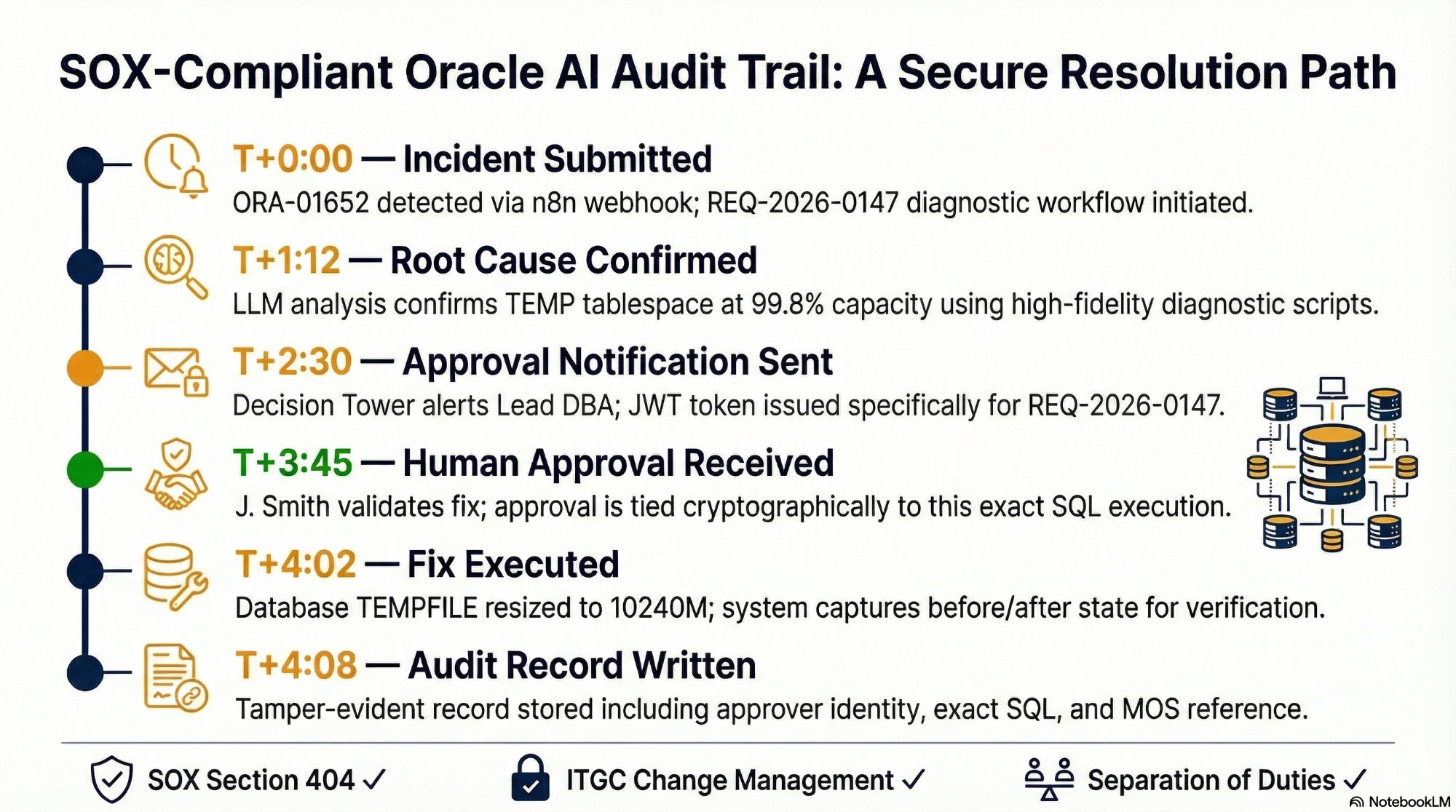
A single ORA-01652 resolution from incident to audit record — 4 minutes 8 seconds, fully documented. Every step is timestamped, the human approval is cryptographically tied to the exact SQL executed, and the final record satisfies SOX Section 404, ITGC Change Management, and Separation of Duties requirements.
What SOX Actually Requires
SOX Section 404 requires that management assess the effectiveness of internal controls over financial reporting. For Oracle EBS environments, this translates into several specific ITGC (IT General Controls) requirements that auditors check every year:
- Changes to production systems must be authorized by an appropriate approver before implementation
- The approver and the person implementing the change must be different individuals (separation of duties)
- A documented record must exist showing what changed, who authorized it, and when
- Emergency changes must be reviewed and approved after the fact if implemented without advance authorization
- Access to make system changes must be restricted to authorized individuals
Manual DBA processes satisfy these controls inconsistently. A DBA who diagnoses a problem and fixes it in the same session is both the implementer and — implicitly — the authorizer. The change record is often a Jira ticket with a comment that says "extended TEMP tablespace, monitoring." An auditor looking for documented pre-implementation authorization will not find it.
The Platform's Audit Record Schema
Every High-Risk action executed by the Oracle AI platform generates a signed audit record written to the Postgres store immediately after execution. The schema is designed to satisfy every ITGC Change Management requirement without additional documentation work from the DBA team.
The record captures: the unique Request ID linking the incident, diagnostic output, approval decision, and execution into a single auditable event; the identity of the executing agent (the Oracle AI platform, not a named individual — because the AI does not make the authorization decision); the identity and timestamp of the human approver, JWT-verified at execution time; the exact SQL command that executed — verbatim, not a description; the LLM reasoning summary documenting the evidence chain that produced the fix recommendation; and the before/after system state captured immediately before and after execution.
This is not a log entry. It is a complete change record that demonstrates authorization (approver identity + JWT verification), separation of duties (AI proposes, human approves, platform executes — no single person does all three), documentation (exact SQL + evidence chain), and timing (the approval timestamp is always before the execution timestamp).
The platform enforces separation of duties architecturally, not by policy. The diagnostic Oracle connection is read-only — it cannot execute a fix. The execution connection requires a validated JWT from the approval workflow. No single individual has both diagnostic access and unrestricted execution access. The AI agent cannot approve its own fix recommendations. These are structural constraints.
The JWT Approval Signal
The JWT (JSON Web Token) mechanism deserves specific attention because it is what makes the approval record verifiable rather than self-reported. When the lead DBA clicks Approve in the Decision Tower notification, the approval signal carries a JWT token that encodes the approver's identity, the specific Request ID being approved, and a timestamp. The token is signed with a secret that only the n8n instance holds.
Before executing any High-Risk fix, n8n validates the JWT. It checks that the token was issued for this specific Request ID — preventing a captured approval signal from being replayed against a different incident. It checks the approver's identity against the authorized approver list. It confirms the token has not expired. Only then does the execution proceed.
This means the audit record's approver field is not self-reported — it cannot be modified by the DBA after the fact, it cannot be fabricated, and it is tied to the exact SQL that executed. An auditor can verify the complete chain: this person approved this specific fix at this specific time, and this specific SQL ran as a result.
Green and Amber Tier Records
Green tier (read-only diagnostic) actions also generate audit records — lighter-weight entries that document what scripts ran, what the output was, and what report was delivered to the user. These satisfy the logging requirements for read access to financial systems.
Amber tier (auto-execute with rollback) actions generate full execution records including the rollback command that was available. If an Amber action is rolled back, the rollback event is recorded as a separate entry linked to the original execution record — providing a complete picture of both the action and its reversal.
What This Means for Annual Audit Preparation
For an Oracle EBS environment running the AI platform, ITGC audit preparation changes significantly. Instead of reconstructing what happened to the production database over the past year from DBA memory and Jira comments, the compliance team can query the Postgres audit store directly. Every production change has a complete record with JWT-verified authorization, exact SQL, and before/after state.
The audit trail is not a side effect of the platform — it is produced automatically as part of every execution path. The DBA team does not spend time documenting changes after the fact because the documentation is generated at the moment of execution. The compliance team does not have to take the DBA's word for what changed because the platform's records are tamper-evident and cryptographically tied to the approval events.
Autonomous Oracle support and SOX compliance are not in conflict. The platform is designed so that automation makes the audit trail better, not worse — more complete, more consistent, and more verifiable than the manual processes it replaces.