The Traffic Light Framework
Risk classification happens automatically at the point of triage — before any diagnostic script runs. The classification determines what happens at the end of the workflow: autonomous execution, auto-execution with rollback, or a full human approval gate.
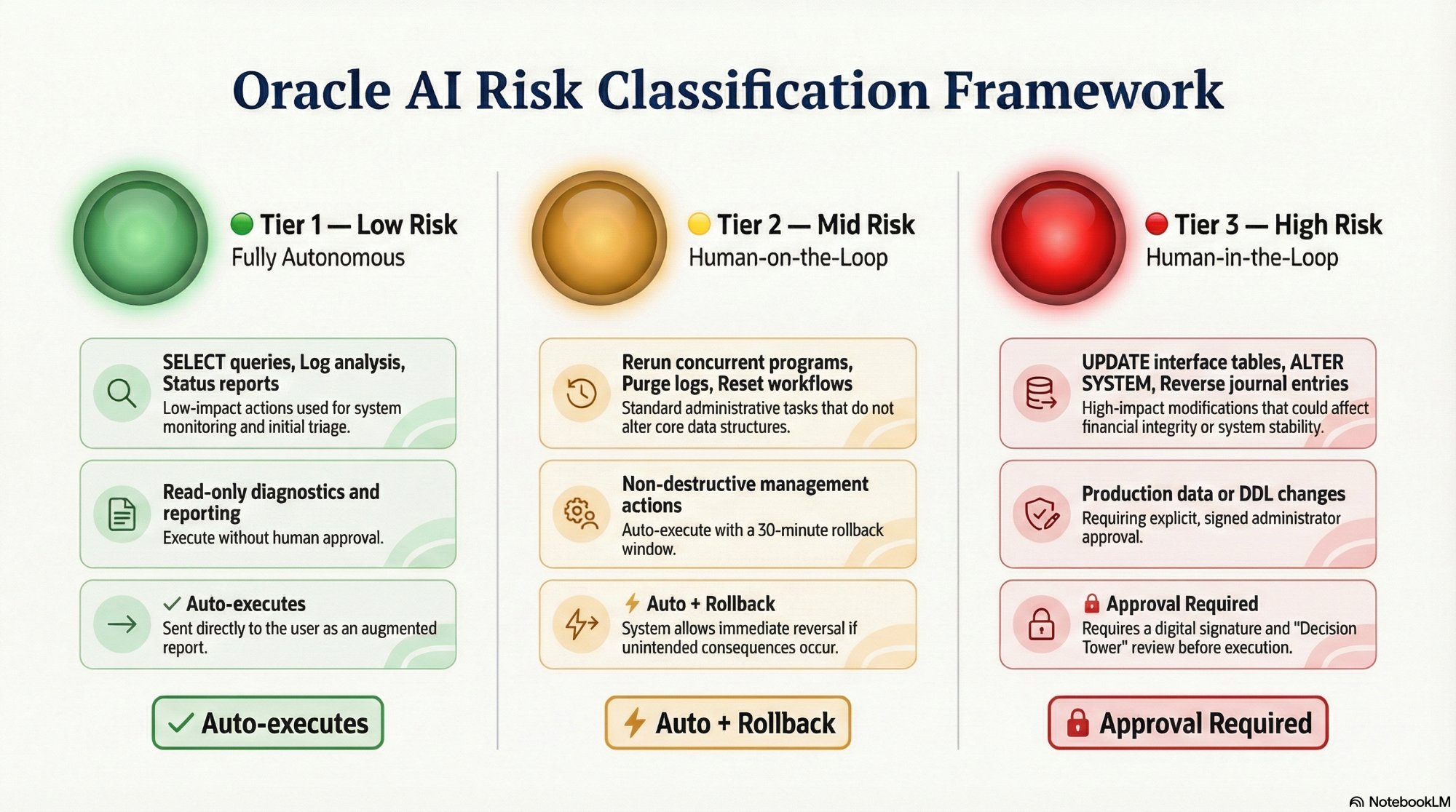
The three-tier risk classification framework. Every Oracle action is classified before execution — the tier determines whether it runs autonomously, with a rollback window, or requires signed human approval.
Fully Autonomous
Read-only diagnostic and reporting actions. No data is modified, no configuration is changed. The platform executes and delivers the augmented report directly to the user. No approval step.
FROM dba_tablespace_usage_metrics;
AP Invoice Hold report query
GL Period open/close status check
Human-on-the-Loop
Non-destructive management actions with no permanent data changes. Auto-execute with immediate effect, but an Instant Rollback button remains active for a configurable window (default: 30 minutes).
Purge old log files from spool;
Reset stuck workflow activity.
Human-in-the-Loop
Any action touching production data, system configuration, or DDL-level database changes. The platform serializes complete state and holds indefinitely — no timeout path exists that auto-executes without a signed human decision.
ALTER SYSTEM extend tablespace;
Reverse posted GL journal entry.